Threat Analysis: Investigating Suspicious Outbound Connections to cdn.jsdelivrs[.]com (Adware or Supply Chain Foothold?)
![Threat Analysis: Investigating Suspicious Outbound Connections to cdn.jsdelivrs[.]com (Adware or Supply Chain Foothold?)](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1753931320526%2F96970cc3-2372-4aa3-a7ef-79db43716d51.png&w=3840&q=75)
Alert Overview
On May 8, 2025, analysts at the FPT SOC identified a cluster of outbound HTTP requests from several internal endpoints targeting the domain cdn.jsdelivrs[.]com. This domain, which resolves to IP 91.195.240.12, is registered under AS47846 (SEDO GmbH, Germany). Although seemingly benign at first glance, the domain closely resembles the legitimate jsDelivr CDN (cdn.jsdelivr.net) and triggered concern due to its typosquatted naming and non-standard usage patterns.
Initial review of DNS and proxy logs revealed browser-driven connections without any indication of direct user interaction with the domain itself, suggesting script-initiated activity embedded within a third-party webpage.
Investigation Details
1. Initial Analysis
Firstly, we found that all the affected hosts that accessed the same URL accessed the website sports[.]ltn[.]com[.]tw, a Taiwanese sports news website.
After checking the embedded JavaScript within the page invoked pop-up ads, one of which triggered the suspicious request to cdn.jsdelivrs[.]com.


App AnyRun Sandbox Result: https://app.any.run/tasks/90532748-66f1-4d09-a90e-d1ca27bd3f35
The flow appeared entirely browser-driven, with the endpoint process tree linking to chrome.exe, no CLI usage observed.
2. Domain Intelligence (WHOIS + Passive DNS)
| Attribute | Value |
| Queried Domain | cdn.jsdelivrs[.]com |
| IP Address | 91.195.240.12 |
| ASN / Org | AS47846 / SEDO GmbH |
| Passive DNS | \>120 subdomain queries in past 180 days |
| WHOIS Created | 2017, tagged as monetized/parked domain |
| SSL Certificate | Self-signed, non-validating |
The domain is a typosquatted clone with no legitimate CDN functions. Historical associations tie it to ad redirect platforms, SEO manipulation, and domain parking infrastructure.
3. Payload Characteristics
HTTP GET requests to
cdn.jsdelivrs[.]comreturned either empty responses or HTML with redirect scripts.Redirection targets included
sedoparking.comand similar monetization services.No evidence of JavaScript obfuscation, encoded payloads, or exploit delivery.
DPI (where available) confirmed redirection to external parked domains, ~200 byte HTML responses, consistent with advertising scripts.
4. Correlation with jsDelivr Abuse Campaigns
While this specific domain was not directly tied to past phishing infrastructure, its pattern strongly resembles the attack flow documented in the 2023 Check Point report:
Malicious npm package (
reactenz) was used to dynamically load an encoded HTML phishing page hosted on jsDelivr’s CDN.jsDelivr retained the payload even after the source package (
standforusz) was taken down from npm due to permanent caching policies.The phishing flow was only visible at runtime due to obfuscation and dynamic DOM injection.
Assessment: In our case, no phishing payloads or encoded HTML were observed. However, the infrastructure setup (typosquatted domain, parked redirection) could be reused or repurposed with little effort by a motivated actor.
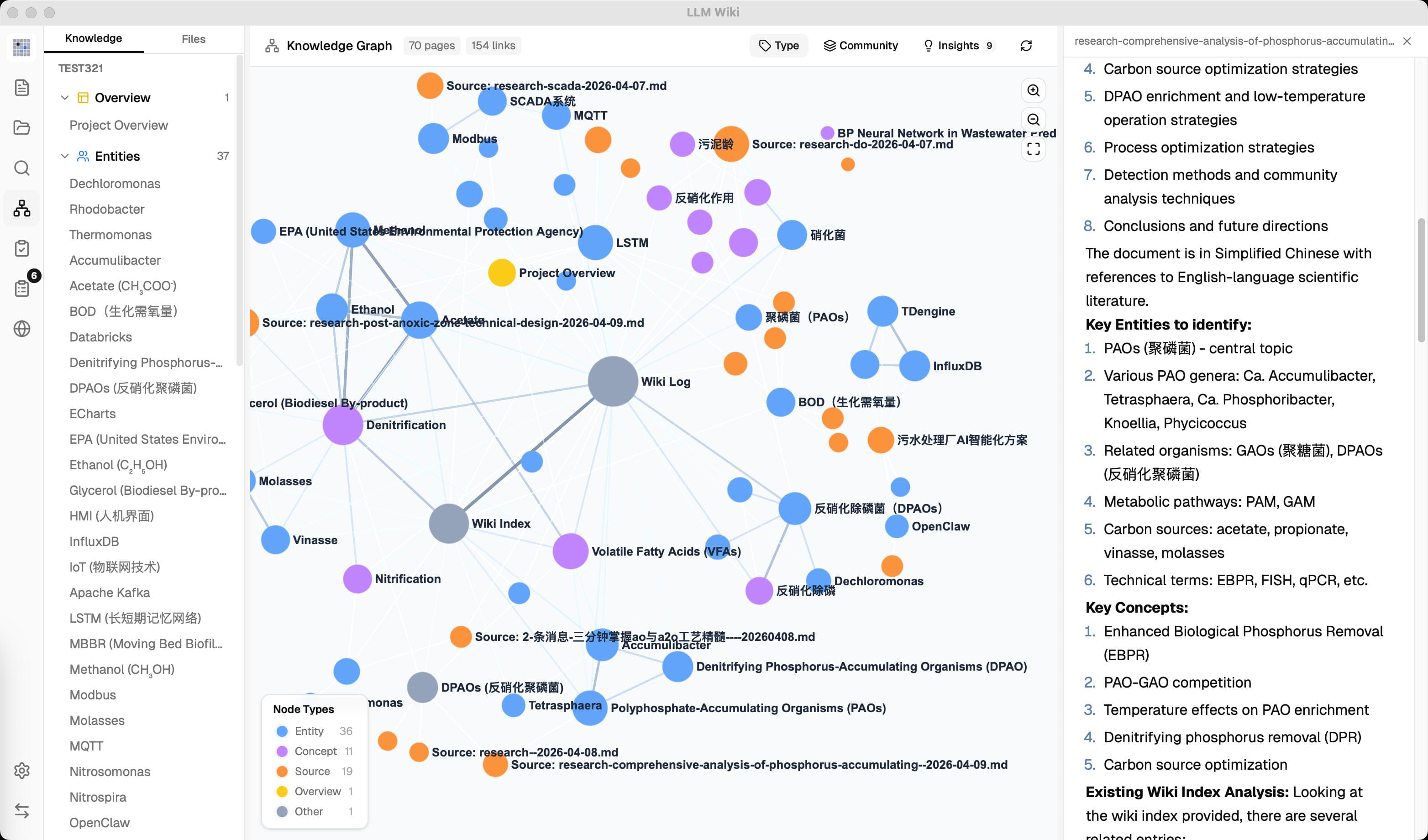
5. Traffic Flow Visualization

The diagram above outlines the interaction chain: a user visits a legitimate website, embedded JavaScript spawns an ad popup that connects to a typosquatted CDN-like domain, returning redirector content. A hypothetical branch illustrates the abuse pathway seen in phishing kits using similar delivery infrastructure.
Actions & Mitigations
| Mitigation Step | Detail |
| Network Enforcement | MDE and firewall enforced a deny policy for all connections to the domain/IP |
| Threat Intel Integration | Domain and IP added to the custom CrowdStrike IOC list |
| IOC Hunt | SIEM queried for the past 30 days across DNS/proxy logs for recurrence |
| Endpoint Process Review | No signs of persistence, scheduled tasks, or PowerShell/scripting activity |
| ATT&CK Mapping | Considered T1566.002 (phishing via service), T1204.001 (user-triggered link) |
📚 References
Check Point Research – "CDN Service Exposes Users to Malicious Packages for Phishing Attacks Invisible to Security Tools"
HackRead – "Global CDN Service ‘jsdelivr’ Exposed Users to Phishing Attacks"
GitHub – jsDelivr Design & File Caching Model